Downloads
4.2 Downloads
Authentication Server 4.2
AuthlogicsAuthenticationServer4.2.1054.0.zip
146.49 MB
Download
Authlogics Password Audit Tool 2.4 (Online Only)
PasswordAuditToolOnlineOnly2.4.5552.1.zip
1.23 MB
download
Authlogics Password Audit Tool 2.4 (Online & Offline)
AuthlogicsPasswordAuditTool2.4.5551.1.zip
12.07 GB
download
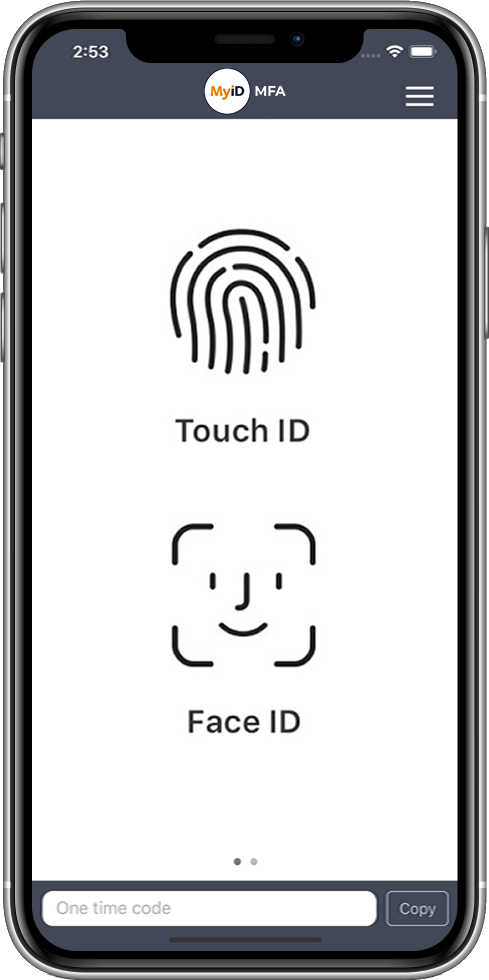
Available from all Major App Stores
Our software tokens work with Authentication Service to turn most electronic devices, including phones, laptops and tablets, into a two factor token. The software is self contained and does not require data connectivity to function, the tokens work completely offline. The software token is free to download and install on laptops and tablets, and freely available in app stores.
Quick Start
Password Security Management Quick Start Guide 4.2
Authlogics-Password-Security-Management-Quick-Start-Guide-4.2.1030.0.pdf
890.41 KB
Download
Multi-Factor Authentication Quick Start Guide 4.2
Authlogics-Multi-Factor-Authentication-Quick-Start-Guide-4.2.1050.0.pdf
1,003.54 KB
download
Authentication Server
Authentication Server Installation and Configuration Guide 4.2
Authlogics-Authentication-Server-Installation-and-Configuration-Guide-4.2.1052.0.pdf
5.96 MB
Download
Authentication Server Developers Guide 4.2
Authlogics-Authentication-Server-Developers-Guide-4.2.1052.0.pdf
789.01 KB
download
Authlogics Self Service Portal User Guide 4.2
Authlogics-Self-Service-Portal-User-Guide-4.2.pdf
803.26 KB
download
Offline Password Breach Database Guide 4.2
Authlogics-Offline-Password-Breach-Database-Guide-4.2.1030.0.pdf
352.21 KB
download
High Availability and Load Balancing Guide 4.2
Authlogics-High-Availability-and-Load-Balancing-Guide-4.2.pdf
404.30 KB
download
System Agents
Windows Desktop Agent Integration Guide 4.2
Authlogics-Windows-Desktop-Agent-Integration-Guide-4.2.1030.0.pdf
1.62 MB
Download
Domain Controller Agent Integration Guide 4.2
Authlogics-Domain-Controller-Agent-Integration-Guide-4.2.1030.0.pdf
622.14 KB
download
ADFS Agent Integration Guide 4.2
Authlogics-ADFS-Agent-Integration-Guide-4.2.1031.0.pdf
2.68 MB
download
Exchange Agent Integration Guide 4.2
Authlogics-Exchange-Agent-Integration-Guide-4.2.1030.0.pdf
564.95 KB
download
Remote Desktop Agent Integration Guide
Remote-Desktop-Agent-Integration-Guide-4.1.3000.0.pdf
406.99 KB
download
MyID Active Directory Password Audit Guide
Active-Directory-Password-Audit-Guide.pdf
614.03 KB
download
Cloud and 3rd Party
Office 365 Integration Guide 4.1
Authlogics-and-Office-365-Integration29158.pdf
131.23 KB
Download
Authlogics SIEM Integration Guide 4.2
Authlogics-SIEM-Integration-Guide-4.2.pdf
444.41 KB
download
YubiKey Reprogramming Guide 4.2
Authlogics-YubiKey-Reprogramming-Guide-4.2.pdf
665.17 KB
download
Authlogics Palo Alto Integration Guide 4.2
Authlogics-Palo-Alto-Integration-Guide-4.2.pdf
294.05 KB
download
Trusted by Governments and Enterprises Worldwide