Banks can do better than biometric authentication alone
In this blog post, originally published in Global Banking and Finance Review, Intercede Chief Product Officer, Allen Storey examines the inherent security vulnerabilities banks face if they rely on biometric authentication alone.
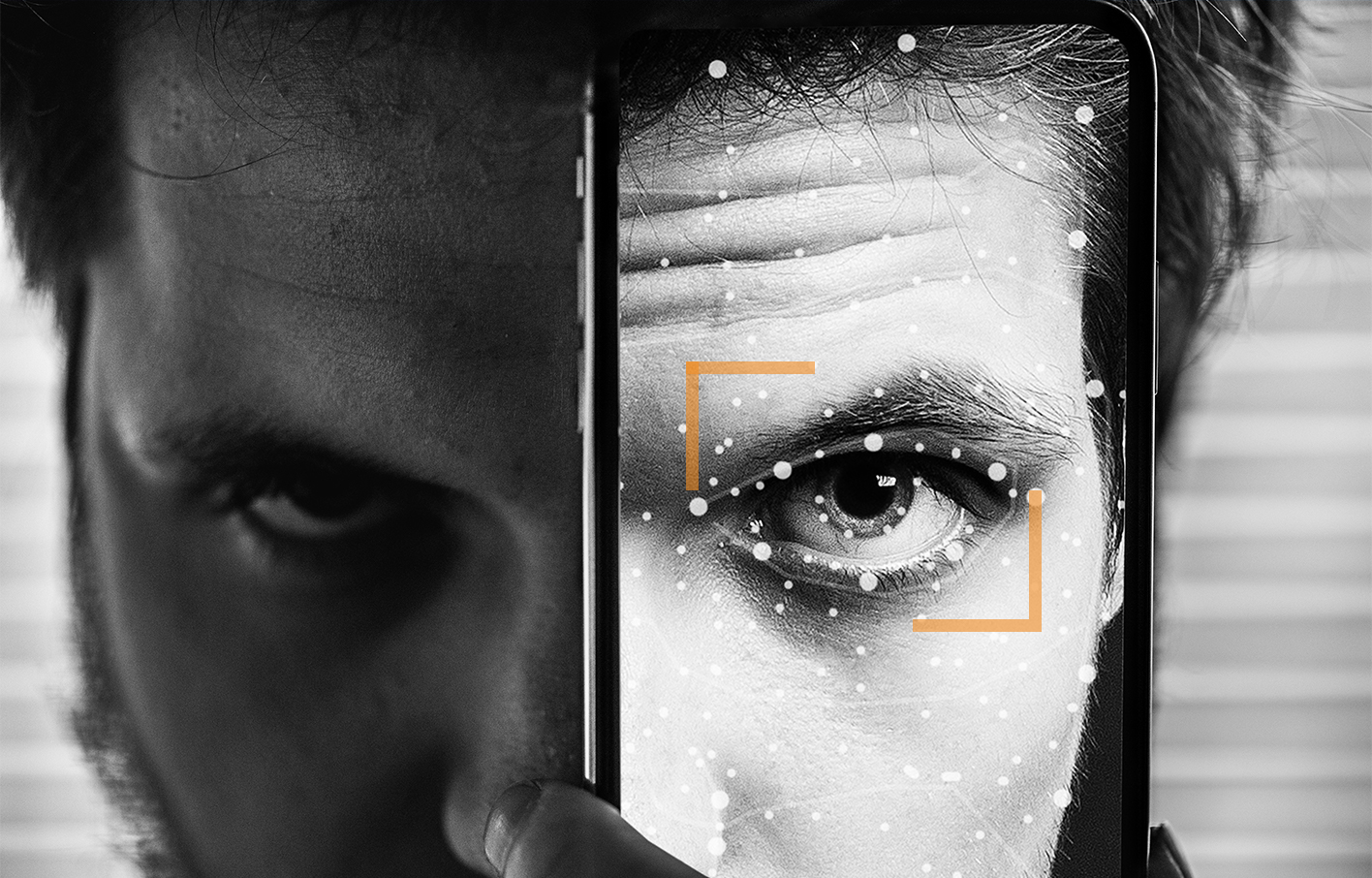
With US regulators questioning its efficacy, and regular reports that everything from photos to siblings can unlock mobile devices via facial recognition, businesses should be looking at stronger methods of authenticating access to their systems and managing credentials of their employees.
Speaking earlier this year at a trade event in Brussels, Alphabet CEO Sundar Pichai added yet another senior voice to the calls for a moratorium on the use of facial recognition, noting the technology is “fraught with risks”. While this focused mainly on the ability for rogue organisations or authoritarian governments to use biometrics for nefarious purposes, the technology is often unreliable, and the platform security is lacking.
Despite these concerns, many of our institutions are still using older, less secure technologies to determine who can and can’t access their premises and networks. As technology advances, so too do the attempts to undermine it. Security technology continues to improve, but hacker’s ability to work around it does too. It is therefore incredibly important for organisations to continuously re-evaluate their systems, updating them regularly to maintain the necessary protections for their data.
While in previous years stronger authentication methods such as Public Key Infrastructure (PKI)-based credentialing was expensive and difficult to deploy in all but the biggest organisations with the largest budgets, recent innovation has made this technology much more accessible.
For financial services organisations, and in particular retail banks, who hold confidential details of people’s finances as well as other personally identifiable information, the ability to hold and use this information without it being shared further or compromised is an inherent part of the service provided to customers.
Within the bank there will be those who require access to certain data sets and those that don’t. For instance, a mortgage adviser would need a detailed picture of an applicant’s finances over a longer time period than most, whereas a customer service representative might only require knowledge of a customer’s account name and number to pass them on to another department or colleague. To manage who can and cannot access certain records most banks will use an Identity and Access Management (IDAM) or Privileged Access Management (PAM) system. While these systems can determine which users have the necessary clearance to access different data sets, they often require another, separate system to authenticate that the person logging in to that user account is the person it has been assigned to. This is where strong employee credentials, that are both unique and bound to them, come in. The combination of these two systems allow banking institutions can ensure they are able to deliver services efficiently while managing customer data securely.
At Intercede we actively encourage IT professionals to move further up the authentication pyramid to ensure their systems are secure and only accessible to those who have explicit approval – protecting themselves from unlawful access by employees, hackers, or even cyberterrorism.
Moving to credentials management systems that enable strong methods of Multi-Factor Authentication (MFA) to verify identity is easier and cheaper than it has ever been. It’s time that the institutions we trust the most roll out up-to-date security measures to protect some of our most personal data.
PKI-based credentialing can be executed today with relatively cost-effective USB tokens such as the YubiKey or even a smartphone app – binding a key to a user identity, and supporting existing security technologies within the business, such as PIN, fingerprint, or facial recognition. This additional step, matching something an employee has (the credentialed device) with something they know (a PIN) and/or something they are (biometric) allows the organisation to be confident that only those authorised to access a network/location are doing so. Much more so that any of the individual technologies in isolation.
With the improvement of end user technologies, such as smartphones and USB tokens, and pre-installed tech like Microsoft’s Windows Hello for Business, crypto-level protection has become far more accessible for organisations of all sizes. Now, with PKI-based credentials management systems, identity can be verified by a wide range of systems, as the public key is contained in the certificate and PKI easily integrates into Microsoft environments using built-in Windows security features.
Without credential management software, managing smartcards and USB tokens at volumes of anything above 500 employees becomes complex and hugely time consuming for IT teams. For retail banks, with hundreds, if not thousands of frontline staff, this would have been an issue. However, new systems that pair a convenient user experience for the employee with a unified central console that allows for the full lifecycle management of credentials for re-issuance, revocation, unlocking, renewing, removing and updating make the prospect of PKI-based identity and access management at scale commercially viable.
This new ability to remove the complexities of managing PKI credentials makes the strongest form of user authentication so much more accessible for enterprises who don’t want to compromise on data security. Whether financial institutions want to issue staff with physical USB tokens or use an app that can be downloaded on to personal smartphones – there are a wide variety of ways they can provide the kind of security customers expect of those they trust to manage their money.
Whether it’s to provide secure network logon, access to customers’ financial data, or even entry in to secure parts of the bank branch which contain physical cash, these newly available solutions make it easy for enterprises of any size and structure to step up to the most secure method of multi-factor authentication across their workforce.
Trusted by Governments and Enterprises Worldwide
Where protecting systems and information really matters, you
will find Intercede. Whether its citizen
data, aerospace and defence systems, high-value financial transactions,
intellectual property or air traffic control, we are proud that many leading
organisations around the world choose Intercede solutions to protect themselves
against data breach, comply with regulations and ensure business continuity.

