Why all IT leaders need to know the authentication pyramid
All great hierarchies need a pyramid, right? The ancient Egyptians, Maslow’s Hierarchy of needs, and of course identity and access management (IAM).
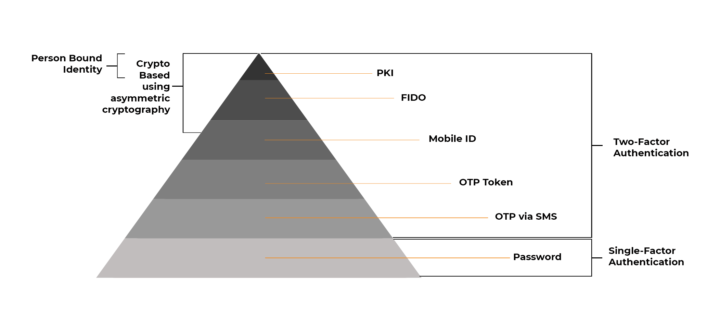
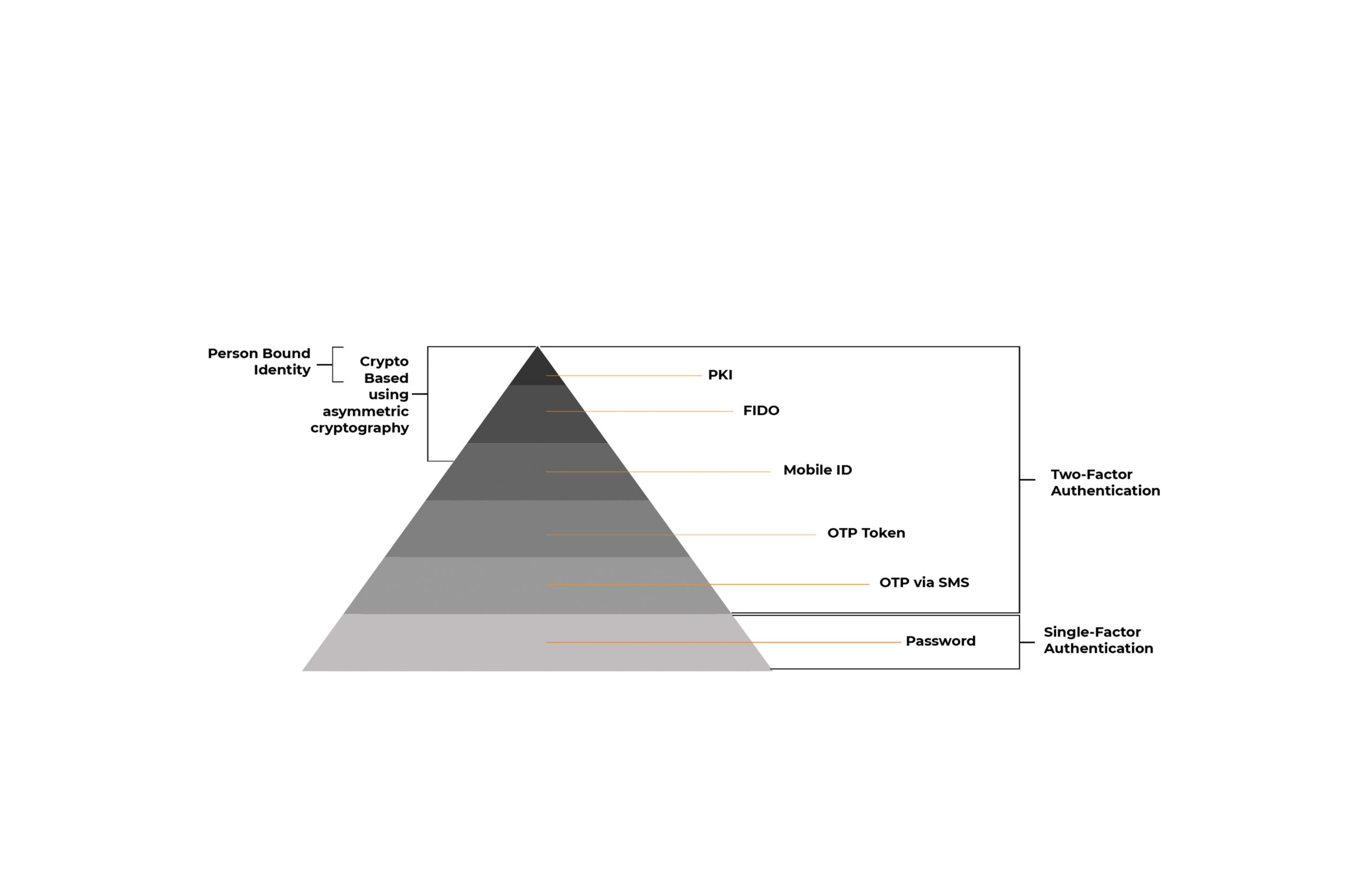
The hierarchy of authentication is a simple way of breaking down the authentication slice of the IAM landscape and categorising available technologies.
There are countless multi-factor authentication vendors out there offering numerous software and hardware but where do they fit and what are the advantages and disadvantages of their technology?
We believe a succinct method of doing just that for Chief Information Security Officers and fellow IT and Information Security professionals, is to use the authentication pyramid.
Fundamentally, we all want to provide a user-friendly means for employees, contractors and suppliers to securely access the information they need as part of their role.
However, in achieving a secure, simple process there are many complexities that need weighing up along the way.
As our matrix shows below, there’s a clear difference between the security offered by OTPs through to PKI. However, implementing strong methods of authentication has typically been complex and so only governments, military, police, aerospace, and defence organisations have adopted such technology.
With technology, such as MyID Professional that has now changed.
| Authentication Method | Advantages | Disadvantages |
|---|---|---|
| Username and Password | • Widely used and familiar to users | • Discredited as insecure • High degree of user inconvenience • High operational cost of resetting forgotten passwords • The number one cause of the majority of data breaches |
| One Time Password via SMS/Message One Time Password (OTP) generated by a server and sent to a mobile device, entered by user and verified by an authentication server | • Perceived simplicity using something the end user already has • No need for client software or dedicated device | • SMS not designed as a secure communications channel • Rogue apps can intercept and forward SMS to an attacker • Can be previewed from an unlocked phone’s screen • User experience is poor, with manual keying required • No direct binding of credential to a user identity • End users not always willing to share personal mobile numbers with their employers for this purpose |
| One Time Password tokens Dedicated device that can generate a one-time password. | • Relatively simple to integrate into an existing environment | • Often relies on symmetric cryptography ‘shared secret key’ which can be compromised • Expensive to distribute at scale • User experience is poor • No direct binding of credential to a user identity |
| Biometrics Use of inherence (something I am) as a second authentication factor - e.g. Fingerprint, facial recognition, voice, iris… | • Growing range of devices now capable of supporting biometrics • User experience is good | • Centralised biometrics can be compromised • Often the platform security is not to the required strength for high security environments • Risk of 'false positive' matches depending on the hardware & software in use • A biometric alone is still only single factor of authentication |
| Push notifications to mobile | • The push mechanism is encrypted, therefore resistant to attack • Familiar user experience | • Although the push notification is secure, the authentication mechanism triggered by it may be less secure • Typically requires an authentication server |
| FIDO Faster IDentity Online, consortium aiming to standardise strong authentication. | • Uses private/public key cryptography for high security • Standards based • Can support PIN, Fingerprint and Face ID so good user experience (device dependent) | • Requires an authentication server • Public key is not directly bound to a user identity, so difficult to prove non-repudiation • Transaction cannot be verified without access to public key, meaning shared usage of a credential is difficult • Cannot be used for signing or encryption without additional solutions |
| PKI & Two Factor Authentication Combines a private key with a public key and certificate issued by a trusted authority. User signs a challenge on their device by providing an authentication factor (typically a PIN number). | • Gold standard solution, proven in the most demanding high security environments – uses private/public key cryptography for high security • User experience is good, can support PIN, fingerprint or Face ID (device dependent) • Certificate binds key to user identity, enabling non-repudiation • Can handle authentication and authorisation via digital signature • Transactions can be verified by any system as the public key is contained in the certificate • Can be used for data encryption • Easy to integrate in Microsoft environments using built-in Windows security features | • Requires a credential management system to issue keys and certificates to secure devices • Requires a Certificate Authority/PKI to be setup and managed |
MyID Professional for accessible PKI-based strong authentication
MyID Professional uses the Microsoft infrastructure that enterprises already have embedded; Microsoft Certificate Services and Microsoft Active Directory, making it far simpler to reach the top of the authentication pyramid.
With MyID Professional integrating into the IT infrastructure, organisations are able to then start issuing certificates to employee smart cards from a variety of manufacturers (Cryptas, Entrust Datacard, Gemalto, Giesecke & Devrient, Idemia, NXP, SafeNet AT, T-Systems) and USB tokens, such as the YubiKey.
MyID Professional also provides IT teams with the central point to lifecycle manage employee credentials for re-issuance, revocation, unlocking, renewing, removing and updating.
Whether it’s to provide secure Windows and network logon, VPN and remote access, signing and encrypting emails or protecting access to cloud resources, MyID Professional makes it easy for enterprises to step up to the most secure method of two-factor authentication across their workforce.
Available as a subscription-based software product, MyID Professional is available through our channel partners.
Interested in finding out more? Contact us now to find a channel partner near you.
Want to join the Connect Partner Programme? Contact us now to find out more – we are actively searching for integrator and reseller partners in North America, EMEA and APAC.
Trusted by Governments and Enterprises Worldwide
Where protecting systems and information really matters, you
will find Intercede. Whether its citizen
data, aerospace and defence systems, high-value financial transactions,
intellectual property or air traffic control, we are proud that many leading
organisations around the world choose Intercede solutions to protect themselves
against data breach, comply with regulations and ensure business continuity.